by CIRT Team
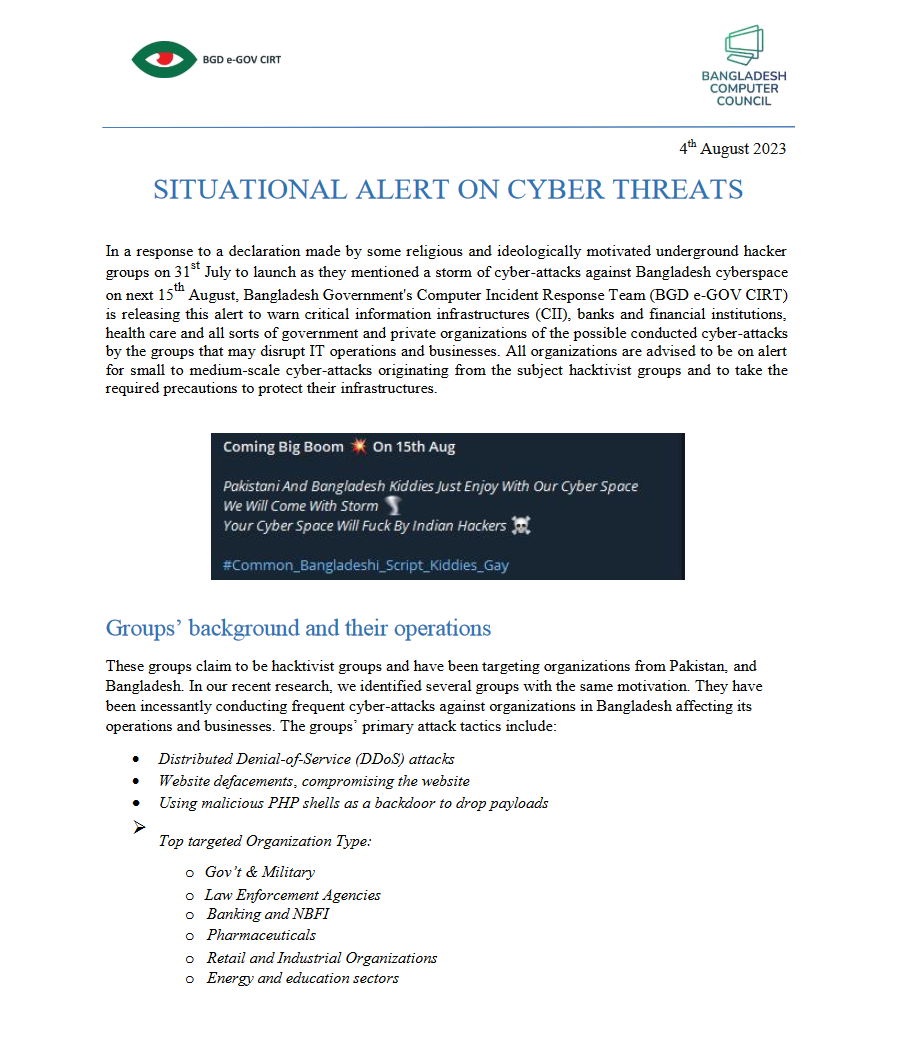
SITUATIONAL ALERT ON CYBER THREATS – August 2023
Get the full PDF Here Get the full PDF Here

by CIRT Team
Press Release: Situational Alert on Cyber Threats, June 2023
Here is the press release. Please click on the document below for full view.
by CIRT Team
Press release April 2023: Situational Security Alerts from CIRT
In the advent of EID holidays, Bangladesh Government’s Computer Incident Response Team (BGD e–Gov CIRT) would like to assure the security of the critical information infrastructures (CII), banks andfinancial institutions, health care and all sorts of government and private organizations by sharing alist of top threats to be vigilant for any suspicious activities in their infrastructure to prevent any sortof intrusion or disruption to their...
Read More

by CIRT Team
Password Policy best practices Create a strong, complex and long password. Use multi-factor authentication for login where possible. Avoid save password in browser. Generic best practices Do not install additional software or server roles on DCs Implement patch management. Use secure DNS services to block malicious domains Ensure business continuity plan (BCP). Use security baselines and benchmarks. Inform and educate users about cyber threats and...
Read More
Dropbox discloses breach after hacker stole 130 GitHub repositories
Dropbox disclosed a security breach after threat actors stole 130 code repositories after gaining access to one of its GitHub accounts using employee credentials stolen in a phishing attack. The company discovered the attackers breached the account on October 14 when GitHub notified it of suspicious activity that started one day before the alert was sent. “To date, our investigation has found that the code...
Read More

ABOUT “BLUEBLEED”SERVICE AND THE VULNERABILITY OF MICROSOFT AWS SERVERS
Attack infoFirst seen 2022-09-24 • Last seen 2022-10-19On October 19, 2022, Socradar announced a vulnerability they discovered in several misconfiguredMicrosoft AWS servers. They also announced the launch of the BlueBleed service, which contains datadownloaded from several misconfigured Microsoft AWS servers.Link to the Socradar announcement – hxxps://socradar[.]io/sensitive-data-of-65000-entities-in-111-countries-leaked-due-to-a-single-misconfigured-data-bucket/ The exposed files in the misconfigured bucket include; POE documents,SOW documents,Invoices,Product orders,Product offers,Project details,Signed customer documents,POC (Proof of Concept)...
Read More

New PHP information-stealing malware targets Facebook accounts
A new Ducktail phishing campaign is spreading a never-before-seen Windows information-stealing malware written in PHP used to steal Facebook accounts, browser data, and cryptocurrency wallets. Ducktail phishing campaigns were first revealed by researchers from WithSecure in July 2022, who linked the attacks to Vietnamese hackers. Those campaigns relied on social engineering attacks through LinkedIn, pushing .NET Core malware masquerading as a PDF document supposedly containing details about a marketing...
Read More

Magniber ransomware now infects Windows users via JavaScript files
A recent malicious campaign delivering Magniber ransomware has been targeting Windows home users with fake security updates. Threat actors created in September websites that promoted fake antivirus and security updates for Windows 10. The downloaded malicious files (ZIP archives) contained JavaScript that initiated an intricate infection with the file-encrypting malware. A report from HP’s threat intelligence team notes that Magniber ransomware operators demanded payment of up to $2,500...
Read More

CVE-2022-41352: Remote Code Execution Vulnerability in Zimbra Collaboration Suite CVSS 3.0: 9.8 (Critical)
Vulnerability DescriptionAn issue was discovered in Zimbra Collaboration (ZCS) 8.8.15 and 9.0. An attacker can upload arbitrary files through amavisd via a cpio loophole (extraction to /opt/zimbra/jetty/webapps/zimbra/public) that can lead to incorrect access to any other user accounts. Zimbra recommends pax over cpio. Also, pax is in the prerequisites of Zimbra on Ubuntu; however, pax is no longer part of a default Red Hat installation...
Read More









