During the past week, an outbreak of Ryuk ransomware that impeded newspaper printing services in the United States has garnered a lot of attention. To determine who was behind the attack many have cited past research that compares code from Ryuk with the older ransomware Hermes to link the attack to North Korea. Determining attribution was largely based on the fact that the Hermes ransomware...
Read More
Description: Drupal has released security updates addressing vulnerabilities in Drupal 7.x, 8.5.x, and 8.6.x. Impact: A remote attacker could exploit this vulnerability to take control of an affected system. Mitigation: Updates are available. Please see the references or vendor advisory for more information. Reference URL’s: https://www.drupal.org/sa-core-2019-001 https://www.drupal.org/sa-core-2019-002
Description: Oracle has released its Critical Patch Update for January 2019 to address 284 vulnerabilities across multiple products. Impact: A remote attacker could exploit this vulnerability to take control of an affected system. Mitigation: Updates are available. Please see the references or vendor advisory for more information. Reference URL’s: https://www.oracle.com/technetwork/security-advisory/cpujan2019-5072801.html
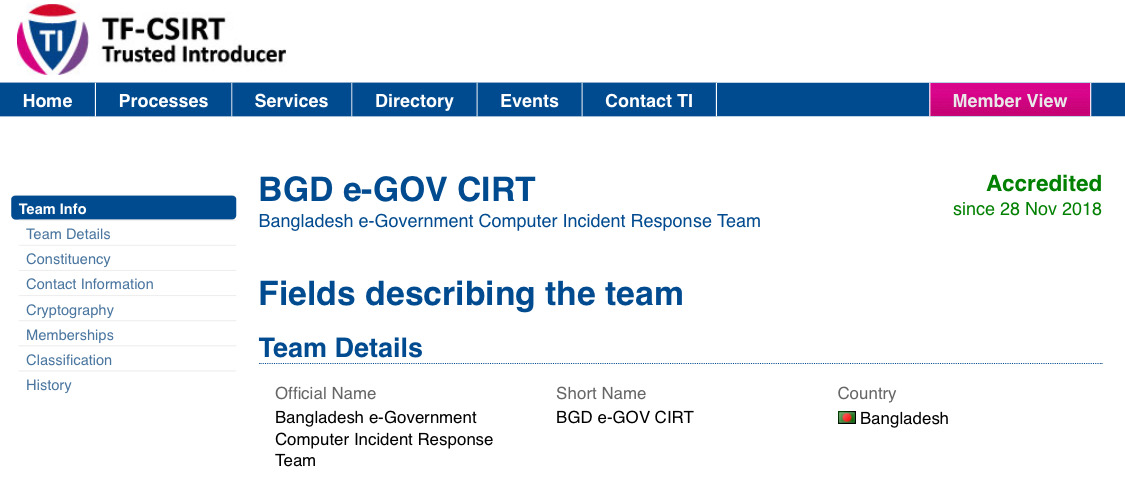
The Trusted Introducer (TI) provides European CSIRTs (Computer Security Incident Response Teams) with a public repository that lists all known European CSIRTs and explains about the TI’s accreditation service. This service is meant to do just that: facilitate trust by formally accrediting CSIRTs that are ready to take that step. Earlier in September 2018, BGD e-GOV CIRT has been “listed” as Trusted Introducer of TF-CSIRT....
Read More
Security researchers have been warning about a simple technique that cybercriminals and email scammers are already being using in the wild to bypass security features of Microsoft Office 365, including Safe Links, which are originally designed to protect users from malware and phishing attacks. Safe Links has been included by Microsoft in Office 365 as part of its ATP (Advanced Threat Protection) solution that works...
Read More
WordPress-related vulnerabilities have seen a 300% increase in 2018 compared to the previous year, a recent study has found. Most of the bugs were in the plugins that extend the functionality of WordPress websites. Powering about 30% of all websites on the internet, WordPress is the most popular content management system (CMS), followed by Joomla and Drupal trailing behind at a safe distance. A product’s...
Read More
Google has removed 85 apps from its Play Store after finding out that they were pushing aggressive, full-screen adware to Android users. With the rise in the mobile market, Adware has become one of the most prevalent mobile threats in the world. Adware has traditionally been used to aggressively push ads like banners or pop-ups on mobile screens to make money for its makers. The...
Read More
Cyber criminals have stolen customer data from the Titan Manufacturing and Distributing company for nearly one year using a malware. Hackers hit the Titan Manufacturing and Distributing company and compromised its computer system to steal customer payment card data for an entire year. Attackers breached into the computer system at Titan Manufacturing and Distributing company to steal customer payment card data for roughly a year. The company...
Read More
Germany has been hit with the biggest hack in its history. A group of unknown hackers has leaked highly-sensitive personal data from more than 100 German politicians, including German Chancellor Angela Merkel, Brandenburg’s prime minister Dietmar Woidke, along with some German artists, journalists, and YouTube celebrities. The leaked data that was published on a Twitter account (@_0rbit) and dated back to before October 2018 includes...
Read More
Description: Juniper Networks has released multiple security updates to address vulnerabilities in various Juniper products. Impact: A remote attacker could exploit this vulnerability to take control of an affected system. Mitigation: Updates are available. Please see the references or vendor advisory for more information. Reference URL’s: https://kb.juniper.net/InfoCenter/index?page=content&channel=SECURITY_ADVISORIES