Hackers Using Zero-Width Spaces to Bypass MS Office 365 Protection [source: thehackernews]
by CIRT Team
Security researchers have been warning about a simple technique that cybercriminals and email scammers are already being using in the wild to bypass security features of Microsoft Office 365, including Safe Links, which are originally designed to protect users from malware and phishing attacks.
Safe Links has been included by Microsoft in Office 365 as part of its ATP (Advanced Threat Protection) solution that works by replacing all URLs in an incoming email with Microsoft-owned secure URLs.
Therefore, every time users click on a link provided in an email, Safe Links first sends them to a Microsoft owned domain, where it immediately checks the original link for anything suspicious. If Microsoft’s security scanners detect any malicious element, it then warns the users about it, and if not, it redirects them to the original link.
However, researchers at the cloud security company Avanan have revealed how attackers have been bypassing both Office 365’s URL reputation check and Safe Links URL protection features by using Zero-Width SPaces (ZWSPs).
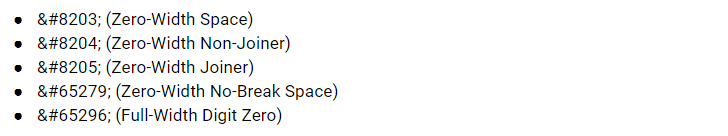
Supported by all modern web browsers, zero-width spaces (listed below) are non-printing Unicode characters that typically used to enable line wrapping in long words, and most applications treat them as regular space, even though it is not visible to the eye.
Zero-Width Space Phishing Attack Demonstration
According to the researchers, attackers are simply inserting multiple zero-width spaces within the malicious URL mentioned in their phishing emails, breaking the URL pattern in a way that Microsoft does not recognize it as a link.
For more, click here.
Recommended Posts

Training on cybersecurity awareness for Department of Women Affairs
25 Nov 2023 - Articles, English articles, News, News Clipping, Service











