WordPress phishing scam targets the database credentials of the users [source: 360totalsecurity]
by CIRT Team
Recently, there has been a phishing email for WordPress users. The content of the email is to inform the users that their database needs to be updated, as shown in the figure below:
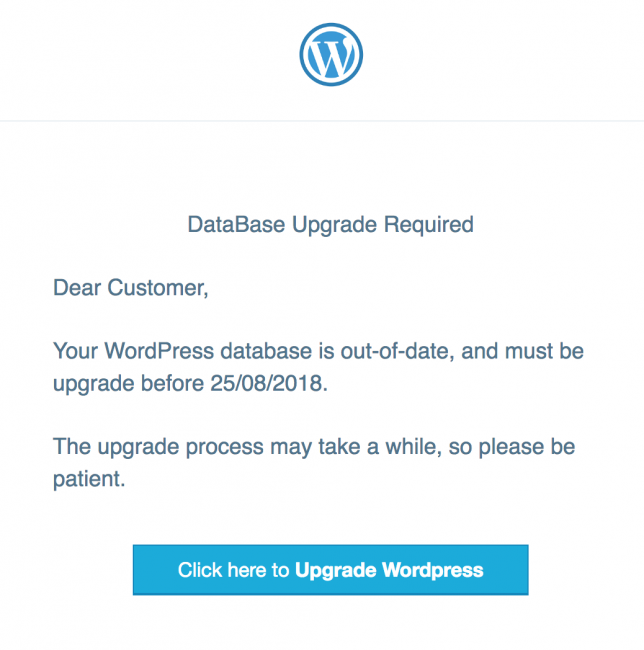
Although the email is similar to a legitimate WordPress update, there are still a number of vulnerabilities: the content contains typos and the message delivery method is older. The deadlines marked in the emails are also suspicious. WordPress officials have previously defined deadlines based on effective explanations, thus, such emails are also difficult to convince service providers. The bigger flaw is that phishing attackers even send timestamps with European formats to the users in the United States.
The footer of the email mimics the habit of Automattic (the parent company of WordPress.com, Jetpack, WooCommerce), but the link also accesses to a phishing page on another hacked website (also located at /so/subdirectory).
For more, click here.
Recommended Posts

Training on cybersecurity awareness for Department of Women Affairs
25 Nov 2023 - Articles, English articles, News, News Clipping, Service











