Worok: A New Cyber Espionage Group Targeting Private and Local Government Entities Mostly in Asia
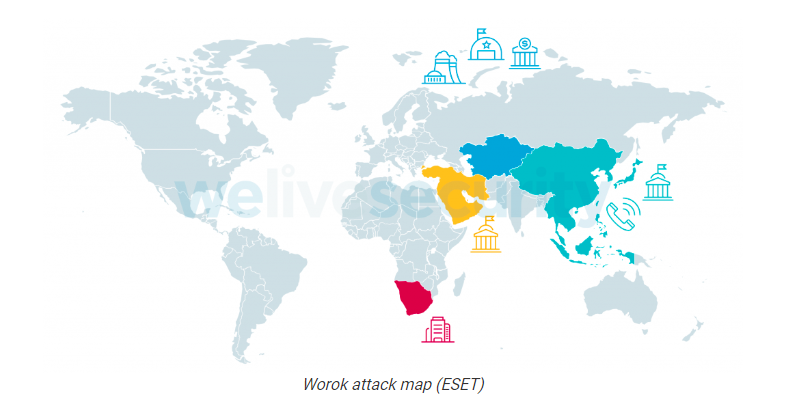
A new cyber espionage threat group that has been previously unknown named Worok and has been observed using undocumented tools targeting private and local government entities mostly in Asia.
Based on the report by ESET, the group has been active for at least 2020 and observed a significant break in operation from 2021-05 to 2022-01, but in 2022-02, their operation resumed, targeting an energy company, and a public sector entity in Southeast Asia.
______________________________
A. Nature of the Attack
Mostly, the method used to gain initial access to its victim’s network was still unknown, in some cases, the group was observed using ProxyShell vulnerabilities. Then later they will use various tools to gain persistence in the network.
Once the adversaries gain access to the network, they will deploy multiple, publicly available tools for reconnaissance, including Mimikatz, EarthWorm, ReGeorg, and NBTscan, and then deployed their custom implants: a first-stage loader, followed by a second-stage .NET loader (PNGLoad). Unfortunately, ESET Security has not been able to retrieve any of the final payloads. In 2021, the first-stage loader was a CLR assembly (CLRLoad), while in 2022 it has been replaced, in most cases, by a full-featured PowerShell backdoor (PowHeartBeat).
First-Stage Loader Tool
- CLRLoad: CLR assembly loader
CLRLoad is a generic Windows PE that we have seen in both 32-and 64-bit versions. It is a loader written in C++ that loads the next stage (PNGLoad), which must be a Common Language Runtime (CLR) assembly DLL file. That code is loaded from a file located on disk in a legitimate directory, presumably to mislead victims or incident responders into thinking it is legitimate software.
- PowHeartBeat: PowerShell backdoor
PowHeartBeat is a full-featured backdoor written in PowerShell, obfuscated using various techniques such as compression, encoding, and encryption. Based on ESET telemetry, we believe PowHeartBeat replaced CLRLoad in more recent Worok campaigns as the tool used to launch PNGLoad.
The PowHeartBeat backdoor uses HTTP to communicate with the C&C Server and later until version 2.4, it was replaced by ICMP.
Once the first stage loader was successfully deployed either by CLRLoad or PowHeartBeat, a second-stage payload will deploy by Worok dubbed as PNGLoad.
Second-Stage Loader Tool
- PNGLoad: Steganographic loader
PNGLoad is a loader that uses bytes from PNG files to create a payload to execute. It is a 64-bit .NET executable – obfuscated with .NET Reactor – that masquerades as legitimate software.
______________________________
B. Indicators of Compromised
List of Indicators of Compromised can be viewed on the link below.
- Official Report of ESET: <https://www.welivesecurity.com/2022/09/06/worok-big-picture/>
- GitHub Repository: <https://github.com/eset/malware-ioc/tree/master/worok>
______________________________
C. Actions to be Taken
CERT-PH recommends the following actions be taken:
- Proactively monitor and secure identified systems and devices for any suspicious/malicious activities.
- Regularly check and apply the latest patch of software, especially to public-facing applications.
- Perform a backup of data regularly and ensure it is encrypted.
- In addition, providing and capacitating employees with cybersecurity knowledge and information to minimize the attack surface.
- For additional information, kindly refer to the official report
- https://www.welivesecurity.com/2022/09/06/worok-big-picture
- https://www.ncert.gov.ph/2022/09/07/worok-a-new-cyber-espionage-group-targeting-private-and-local-government-entities-mostly-in-asia/










