Multiple Vulnerabilities in Cisco Webex Network Recording Player
by CIRT Team
Description: Multiple vulnerabilities in the Cisco Webex
Network Recording Player and Cisco Webex Player could allow an
unauthenticated, remote attacker to execute arbitrary code on the
system of a targeted user. An attacker could exploit these
vulnerabilities by sending a user a link or email attachment
containing a malicious ARF (Advanced Recording Format) or WRF
(Webex Recording Format) file via a link or an email attachment
and persuading the user to open the file with the affected
software.
Impact: Successful exploitation of these vulnerabilities
could allow the attacker to execute arbitrary code on the user’s
system. Depending on the privileges associated with the user, an
attacker could then install programs; view, change, or delete
data; or create new accounts with full user rights. Users whose
accounts are configured to have fewer user rights on the system
could be less impacted than those who operate with administrative
user rights.
System Affected:
* Cisco Webex — all Webex Network Recording Player and Webex
Player releases earlier than Release WBS 39.5.17 or WBS 39.11.0
* Cisco Webex Meetings Online — all Webex Network Recording Player
and Webex Player releases earlier than Release 1.3.49
* Cisco Webex Meetings Server — all Webex Network Recording Player
releases earlier than Release 3.0MR3SecurityPatch1 and
4.0MR2SecurityPatch2
Mitigation:
The following actions are recommended:
* Install the update provided by Cisco immediately after
appropriate testing.
* Run all software as a non-privileged user (one without
administrative privileges) to diminish the effects of a successful
attack.
* Remind users not to visit websites or follow links provided by
unknown or untrusted sources.
* Inform and educate users regarding the threats posed by
hypertext links contained in emails or attachments especially from
un-trusted sources.
* Apply the Principle of Least Privilege to all systems and
services.
Reference URL’s:
https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20200304-webex-player
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-3127
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-3128
Recommended Posts
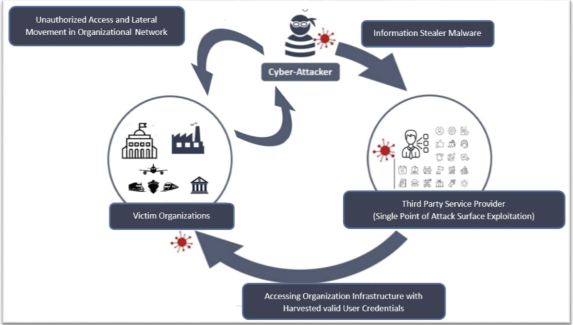
Cyber Threat Alert: Surge in Attacks via Compromised Third-Party Service Providers
08 Feb 2024 - Articles, English articles, Security Advisories & Alerts