Critical Alert: Multiple Vulnerabilities in PHP Could Allow for Arbitrary Code Execution
by CIRT Team
Description: Multiple vulnerabilities have been discovered in PHP, the
most severe of which could allow an attacker to execute arbitrary code.
PHP is a programming language originally designed for use in web-based
applications with HTML content. PHP supports a wide variety of platforms
and is used by numerous web-based software applications.
Impact: Successfully exploiting the most severe of these vulnerabilities
could allow for arbitrary code execution in the context of the affected
application. Depending on the privileges associated with the
application, an attacker could install programs; view, change, or delete
data; or create new accounts with full user rights. Failed exploitation
could result in a denial-of-service condition.
System Affected:
- PHP 7.2 prior to 7.2.3
- PHP 7.0 prior to 7.0.28
- PHP 5.0 prior to 5.6.34
Mitigation:
The following actions are recommended:
- Upgrade to the latest version of PHP immediately, after appropriate testing.
- Verify no unauthorized system modifications have occurred on system before applying patch.
- Apply the principle of Least Privilege to all systems and services.
- Remind users not to visit websites or follow links provided by unknown or untrusted sources.
Reference URL’s:
- http://php.net/ChangeLog-7.php#7.2.3
- http://php.net/ChangeLog-7.php#7.0.28
- http://php.net/ChangeLog-5.php#5.6.34
- http://php.net/ChangeLog-7.php#7.1.15
Recommended Posts
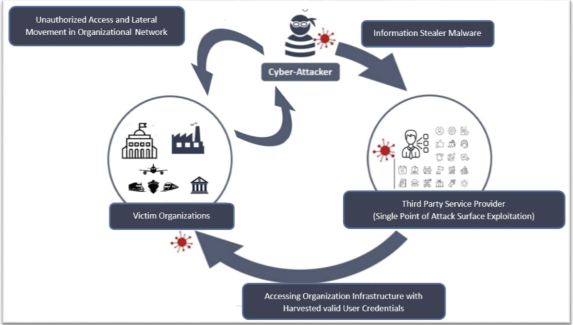
Cyber Threat Alert: Surge in Attacks via Compromised Third-Party Service Providers
08 Feb 2024 - Articles, English articles, Security Advisories & Alerts