Cisco Aironet 1800, 2800, and 3800 Series Access Points Secure Shell Privilege Escalation Vulnerability
by CIRT Team
Description: A vulnerability in the assignment and management of default user accounts for Secure Shell (SSH) access to Cisco Aironet 1800, 2800, and 3800 Series Access Points that are running Cisco Mobility Express Software could allow an authenticated, remote attacker to gain elevated privileges on an affected access point.
Impact: The vulnerability exists because the Cisco Mobility Express controller of the affected software configures the default SSH user account for an access point to be the first SSH user account that was created for the Mobility Express controller, if an administrator added user accounts directly to the controller instead of using the default configuration or the SSH username creation wizard. Although the user account has read-only privileges for the Mobility Express controller, the account could have administrative privileges for an associated access point. An attacker who has valid user credentials for an affected controller could exploit this vulnerability by using the default SSH user account to authenticate to an affected access point via SSH. A successful exploit could allow the attacker to log in to the affected access point with administrative privileges and perform arbitrary administrative actions.
Vulnerable Products
- Aironet 1800 Series Access Points that are running Cisco Mobility Express Software Releases 8.2.121.0 through 8.5.105.0
- Aironet 2800 Series Access Points that are running Cisco Mobility Express Software Releases 8.3.102.0 through 8.5.105.0
- Aironet 3800 Series Access Points that are running Cisco Mobility Express Software Releases 8.3.102.0 through 8.5.105.0
Mitigation: Cisco has released software updates that address this vulnerability. Please see the references or vendor advisory for more information.
Reference URL’s:
- https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20180502-aironet-ssh
- https://cve.mitre.org/cgi-bin/cvename.cgi?name=2018-0226
Recommended Posts
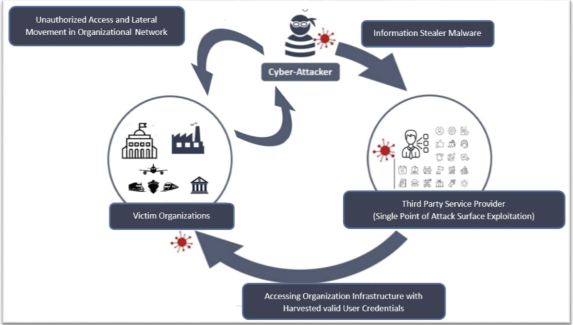
Cyber Threat Alert: Surge in Attacks via Compromised Third-Party Service Providers
08 Feb 2024 - Articles, English articles, Security Advisories & Alerts