by CIRT Team
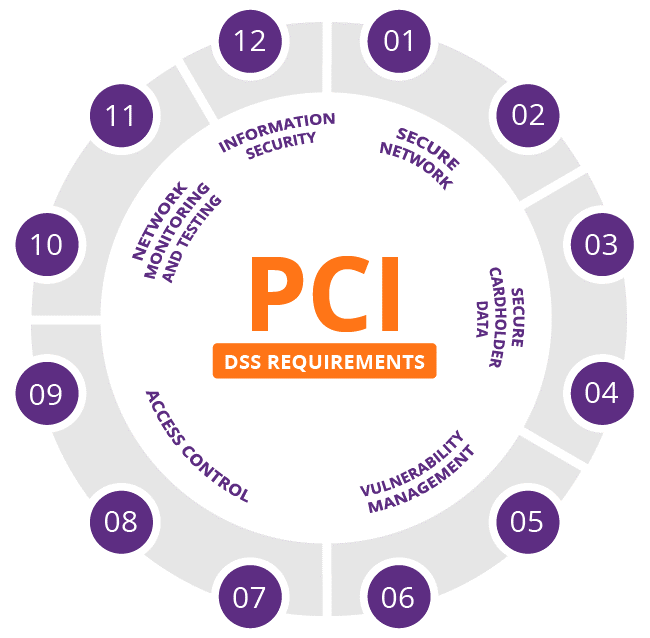
PCI DSS: Basic Information, Certification, Compliance level & Requirement
What is PCI DSS? The Payment Card Industry Data Security Standard (PCI DSS) is a set of security standards formed in 2004 by Visa, MasterCard, Discover Financial Services, JCB International and American Express. Governed by the Payment Card Industry Security Standards Council (PCI SSC), the compliance scheme aims to secure credit and debit card transactions against data theft and fraud. While the PCI SSC has...
Read More
by CIRT Team
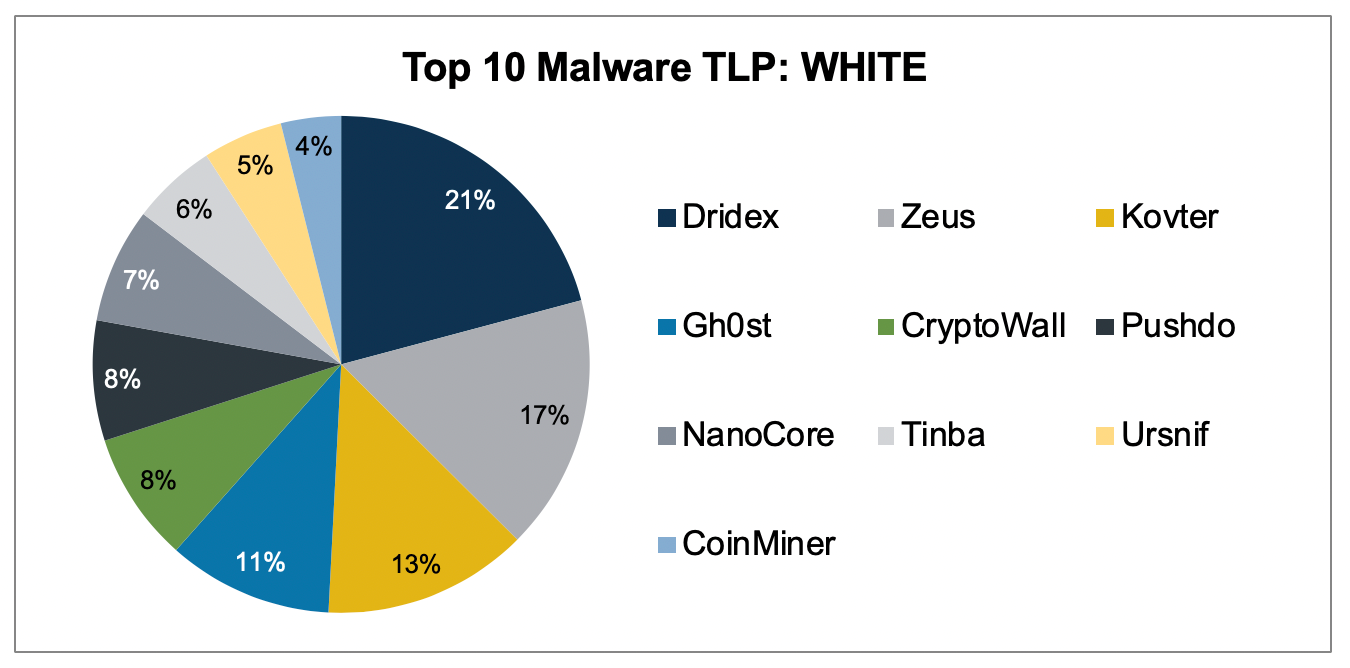
Top 10 Malware March 2020
Top 10 Malware composition was consistent with February 2020 with the exception of Pushdo and Tinba. Overall, the Top 10 Malware variants comprised 42% of Total Malware activity in March, down from 51% in January. It is highly likely that Dridex, Gh0st, Kovter, and ZueS will continue to make up a significant portion of the Top 10 Malware. In March 2020, malware delivered via malspam...
Read More

by CIRT Team
APCERT CYBER DRILL 2020 “BANKER DOUBLES DOWN ON MINER”
Dated : 11 March 2020 The Asia Pacific Computer Emergency Response Team (APCERT) today has successfully completed its annual drill to test the response capability of leading Computer Security Incident Response Teams (CSIRT) within the Asia Pacific economies. The theme of this year’s APCERT Drill is “Banker doubles down on Miner”. This exercise reflects real incidents and issues that exist on the Internet. The participants...
Read More

by CIRT Team
The Effect of Geopolitics on Cybersecurity
The Effect of Geopolitics on Cybersecurity Technological growth and its breakthrough advances, along with their advantages, also have disadvantages, which are obvious examples of communication equipment. In fact, today, the Internet, telephones, cell phones and other communication devices can be described as a double-edged sword used to facilitate communications on the one hand and to spy on and monitor information. The main pillar of cyber...
Read More

by CIRT Team
Role Based Access Control (RBAC) in Elastic Stack
We are all familiar with the Elastic Stack for various purposes. Today, I will let you know about a feature which was previously paid one, but in Elastic Stack 7.0 it has been made free. Role based access control is a feature which will allow users to have permission in specific domain only. This is a must need for a large environment where there are...
Read More
by CIRT Team
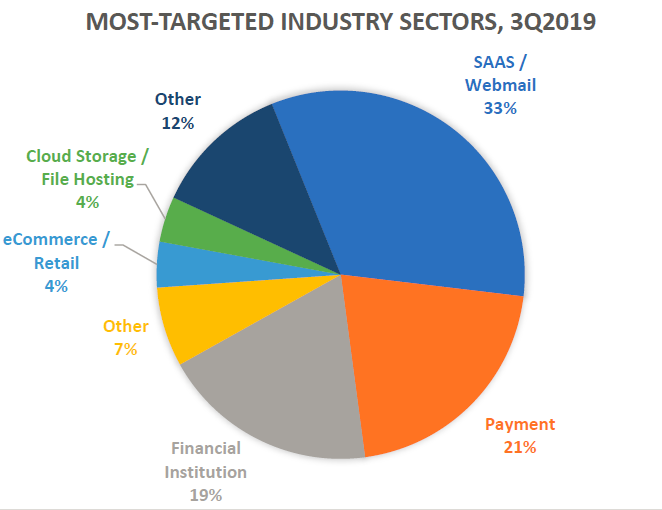
APWG Phishing Activity Trends Reports for Q3’19 Raise Alarm
For a long period of time phishing is one of the major cyber threats in cyberspace. Phishing is the fraudulent attempt to obtain sensitive information such as usernames, passwords and credit card details by disguising oneself as a trustworthy entity in an electronic communication.[1] For past few years we have noticed a rise in the phishing attack in all part of the globe. Anti Phishing...
Read More
by CIRT Team
A Step-By-Step Guide to Securing a Tomcat Server With LetsEncrypt SSL Certificate
Secure Socket Layer (SSL) is a protocol that provides security for communications between client and server by implementing encrypted data and certificate-based authentication. If you’re using Apache Tomcat as a Server for your web-application , chances are that at least some of the data you’re handling is sensitive, and SSL is an easy way to offer your users security. But the configuration process and SSL...
Read More
![2019 CWE Top 25 Most Dangerous Software Errors [mitre]](https://www.cirt.gov.bd/wp-content/uploads/2019/09/2019CWETop25.png)
by CIRT Team
2019 CWE Top 25 Most Dangerous Software Errors [mitre]
Introduction The Common Weakness Enumeration (CWE™) Top 25 Most Dangerous Software Errors (CWE Top 25) is a demonstrative list of the most widespread and critical weaknesses that can lead to serious vulnerabilities in software. These weaknesses are often easy to find and exploit. They are dangerous because they will frequently allow adversaries to completely take over execution of software, steal data, or prevent the software...
Read More

by CIRT Team
Security Tip (ST19-003) Privacy and Mobile Device Apps
What are the risks associated with mobile device apps? Applications (apps) on your smartphone or other mobile devices can be convenient tools to access the news, get directions, pick up a ride share, or play games. But these tools can also put your privacy at risk. When you download an app, it may ask for permission to access personal information—such as email contacts, calendar inputs,...
Read More
by CIRT Team
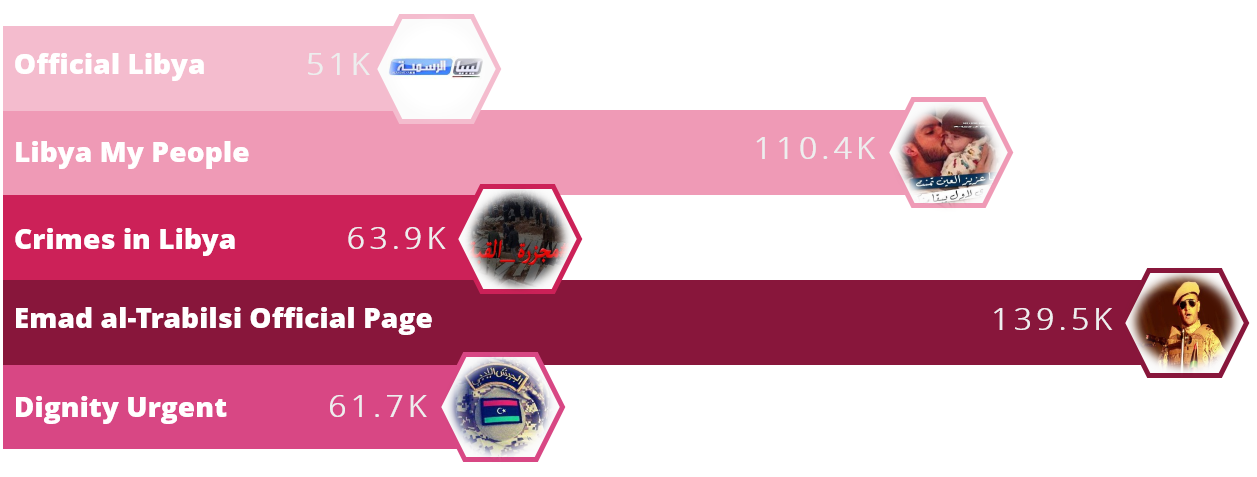
Operation Tripoli
A large-scale campaign has been distributing malware on Facebook for an unspecified number of years primarily targeting the country of Libya, according to Check Point researchers. The threat actors behind this campaign are utilizing the geopolitical and political pages themed around Libya that attempt to convince individuals to download malicious files. Researchers identified more than 30 Facebook pages distributing malicious links and some of the...
Read More










