A Vulnerability in Apache Struts Could Allow for Remote Code Execution
by CIRT Team
DESCRIPTION
A vulnerability has been discovered in Apache Struts, which could allow for remote code execution. Apache Struts is an open source framework used for building Java web applications. Successful exploitation of this vulnerability could allow for remote code execution. Depending on the privileges associated with the user, an attacker could then install programs; view; change, or delete data; or create new accounts with full user rights. Users whose accounts are configured to have fewer user rights on the system could be less impacted than those who operate with administrative user rights.
IMPACT
• Apache Struts versions prior to 2.5.26
SYSTEM AFFECTED
A vulnerability has been discovered in Apache Struts, which could allow for remote code execution. This vulnerability exists due to some of the tag attributes performing a double evaluation if a developer applied forced OGNL evaluation by using the %{…} syntax. Using forced OGNL evaluation on untrusted user input can lead to remote code execution and security degradation. Successful exploitation of this vulnerability could allow for remote code execution. Depending on the privileges associated with the user, an attacker could then install programs; view; change, or delete data; or create new accounts with full user rights. Users whose accounts are configured to have fewer user rights on the system could be less impacted than those who operate with administrative user rights.
RECOMMENDATIONS
Following actions are recommended to be taken:
• Upgrade to the most recent version of Apache Struts after appropriate testing.
• Verify no unauthorized system modifications have occurred on the system before applying the patch.
• Frequently validate type and content of uploaded data.
• Run all software as a non-privileged user (one without administrative privileges) to diminish the effects of a successful attack.
REFERENCES
https://www.cisecurity.org/advisory/a-vulnerability-in-apache-struts-could-allow-for-remote-code-execution_2020-161/
https://cwiki.apache.org/confluence/display/WW/S2-061
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-17530
Recommended Posts
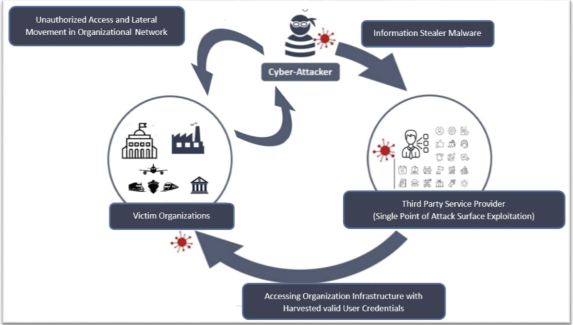
Cyber Threat Alert: Surge in Attacks via Compromised Third-Party Service Providers
08 Feb 2024 - Articles, English articles, Security Advisories & Alerts